Deep State
As I began researching a project about conspiracy theory, paranoia and surveillance I realized my notes and link-lists had taken on an aesthetic that held a narrative distinct from the actual project I was researching. I found this world to be fascinating to I wanted to share my research list for anyone who wants to lose themselves down this rabbit hole.
Manipulation
Psychological Manipulation via Social Media and the concept of self-identity
Social media allows us to increase our social footprint and maintain a steady flow of dopamine but at what cost? To what degree are we insulating ourselves from feeling, training ourselves exclusively for shallow interaction? What is the longterm effect of this optimization? The psychology behind social media interactions.
Strategies advertisers use to sell you products.
6 emotions they determine what you buy. These same emotions seem to influence political decisions
Why facts don't matter
Medium instagram
Fake memes
Wikileaks
Russian oligarchs
Voter targeting
Data collection
Intercept
Facebook failed to protect 10 million of its users
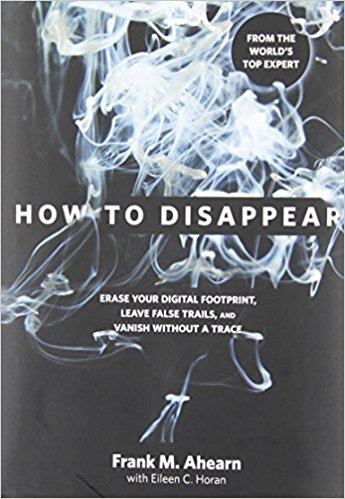
How to lose a tail
How to tail someone
Surveillance techniques
Security & Counter-Surveillance
How to break down a door
Self defense
How to pick a lock
How to hotwire a car
Apophenia is the spontaneous perception of connections and meaningfulness of unrelated phenomena.
The term (German: Apophänie) was coined by psychiatrist Klaus Conrad in his 1958 publication on the beginning stages of schizophrenia. He defined it as "unmotivated seeing of connections [accompanied by] a specific feeling of abnormal meaningfulness".
Our tendency to see patterns
Conspiracy theories?
Confirmation bias: the tendency to interpret new evidence as confirmation of one's existing beliefs or theories.
How to start a revolution
Fun. I’d love to believe this happened but its too easy to fake video. What we observe about the world around us is no longer reliable as evidence.
China has started ranking citizens with a 'social credit' system
Attributable to a strange camera angle or After FX. A Russian dashcam has captured a collision from the most unlikely of angles, making it look as though a car mysteriously appeared from nowhere in the middle of an intersection.
Michael Barkun
Conspiracy theories evolve to incorporate whatever evidence exists against them, so that they become, as Barkun writes, a closed system that is unfalsifiable, and therefore "a matter of faith rather than proof."
Barkun has identified three classifications of conspiracy theory:
Event conspiracy theories. This refers to limited and well-defined events. Examples may include such conspiracies theories as those concerning the Kennedy assassination, 9/11, and the spread of AIDS.
Systemic conspiracy theories. Such theories pertain to alleged broad objectives such as domination of a country or of the world. According to Barkun, the conspiratorial machinery for such theories is usually simple, with a single evil organization. Examples may include conspiracy theories about Jews, Freemasons, Communism, or the Catholic Church.
Superconspiracy theories. For Barkun, such theories link multiple alleged conspiracies together hierarchically. At the summit is a distant but all-powerful evil force. His cited examples are the ideas of David Icke and Milton William Cooper.
Jesse Walker (2013) has identified five kinds of conspiracy theories:
Enemy Outside
Refers to theories based on figures alleged to be scheming against a community from without.
Enemy Within
Finds the conspirators lurking inside the nation, indistinguishable from ordinary citizens.
Enemy Above
Involves powerful people manipulating events for their own gain.
Enemy Below
Features the lower classes working to overturn the social order.
Benevolent Conspiracies
There are angelic forces that work behind the scenes to improve the world and help people.
9/11 Conspiracy theories
https://en.wikipedia.org/wiki/9/11_conspiracy_theories
The people who think 9/11 may have been an 'inside job'
Debunking 9/11 Conspiracy theories
Conspiracy theories
Chinese laser ‘laser AK-47’ sets fire to targets a kilometer away
Sonic attacks in China and Cuba: how sound can be a weapon
Deepfake
"Deepfake, a portmanteau of "deep learning" and "fake", is an artificial intelligence-based human image synthesis technique. It is used to combine and superimpose existing images and videos onto source images or videos."
Changing someone's face in real-time video.
A further corruption of trust in media.
How might this be used for sabotage? Terrorism? To spurn a former lover?
Cryptocurrency
Cryptocurrency Will Replace National Currencies By 2030, According to This Futurist
A distributed ledger (also called a shared ledger, or distributed ledger technology, DLT) is a consensus of replicated, shared, and synchronized digital data geographically spread across multiple sites, countries, or institutions.There is no central administrator or centralized data storage